


Years ago, an old Special Forces team sergeant, Glenn Watson, who did three tours in Vietnam, retired and got a job.
He worked for NEC managing projects that implemented a system called AFIS, or Automated Fingerprint Identification System. Whenever the chance arose, I would go visit my old team sergeant in Georgia or Pennsylvania where he helped install AFIS for each state. Bottom line: during visits Glenn gave me grand tours and “briefings” about how the system works.
Some states were digitizing their massive collections of fingerprint files. Huge amounts data. There were truckloads fingerprint cards in each state. In the old days, police would roll fingerprints on the paper cards, but to link a suspect to a latent print, they needed a clue to an actual suspect, and checking had to be done by hand. So, let’s say a murder occurred and perfect fingerprints were lifted but there was no suspect. The police might have arrested the murderer years ago for something else, so all his data was on file, but for practical purposes, on a national level, the files were unsearchable. Law enforcement would have two perfect dots but no way to connect them.
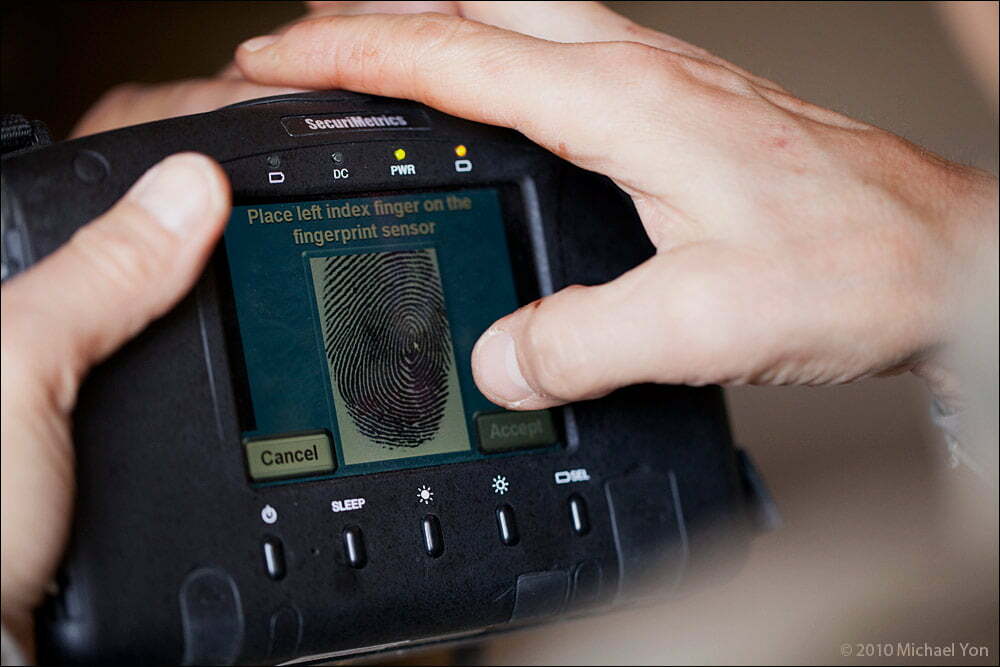
In Atlanta, Glenn showed me a huge room of computer workstations. The air conditioner kept the place very cold, to the point where all the women (most or all were women) who worked there had to wear sweaters or jackets. They were scanning fingerprint cards into the AFIS system and entering the personal information into the data fields. The fingerprints would then pop up on a computer screen (much as seen in these photos with the HIIDE) and the software would do its magic with the minutiae. I was familiar with minutiae and whatnot from Special Forces training; we learned to fingerprint people and how to read the minutiae. The upshot in Atlanta was that after the fingerprints were digitized, law enforcement could cross-check all the “latent prints” (prints left at a crime scene) against the entire database. Glenn said that even as they were still scanning in the truckloads of fingerprint cards, AFIS was getting “hits” on latent prints from crime scenes that were years old. Crimes that would have gone unsolved were suddenly active.

In Iraq, our people were also using these biometrics capture systems. Anyone who was detained/arrested was entered, as was everyone who wanted a job with the Coalition. Data was also collected from bombs, weapons, phones and so forth. During a police recruitment drive in Anbar Province, the applicants were lined up and I recall one scanned in and there was a hit. The soldiers quietly detained him away from the others.


When the HIIDE system is brought back to base, or maybe to a sufficently outfitted vehicle, it can be connected to the main system to download/upload.
Each device has internal memory with a database of photos, retina scans and prints. The computer within the HIIDE will go ahead and scan what is entered against its internal database. So, as our folks scan people in the villagers, if they were to get a hit that matched a latent print from a bomb or a weapon, say, a message would pop up. It could say anything that was entered, such as “DETAIN. Suspected bombmaker,” or, facetiously, “This is Wali Karzai. Let him go.”





No comment yet, add your voice below!